WORKAI® introduces AI for Work — the AI-native approach to Employee Experience
LEARN MORE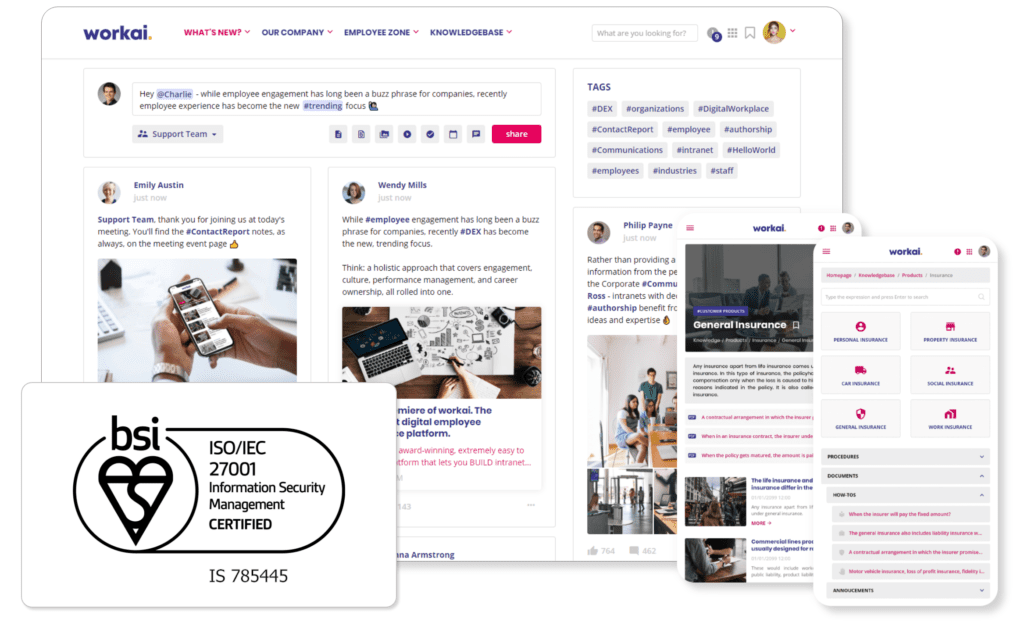
At WORKAI®, we prioritize security and privacy for our diverse industry customer base. Our platform and vision revolve around these crucial aspects, ensuring top-level protection.
Our infrastructure safeguards customer data at every stage, and we provide customizable settings and tools for customers to define their own security parameters.
With WORKAI®’s enterprise-ready support, all customers can trust a secure and reliable platform that meets their needs and concerns.
A copy of the certificate can be found here.
1.1 One of the objectives of the organization is to systematically improve the quality of services provided and the security of designed IT solutions. Ensuring the security of information concerning the data entrusted by customers and the know-how is, among other things, a prerequisite for a successful implementation of this strategy. This is done through the following:
1.1.1 identifying and analyzing information security risks, conducting reviews, and taking actions to reduce them;
1.1.2 creating awareness among employees and sensitizing them to information security issues;
1.1.3 ensuring the physical security of company assets and stored data;
1.1.4 security of Internet links and ICT systems;
1.1.5 appropriate information security regulations in contracts with all stakeholders;
1.1.6 assigning responsibility for ensuring information security;
1.1.7 a systemic approach to information security management.
1.2 The company’s Management Board declares its full commitment to creating conditions for the effective functioning of the ISMS and its improvement. The company’s Management Board undertakes to meet the applicable information security requirements. Thus, it commits all personnel of the organization to apply and comply with the principles of the ISMS.
IISO 27001 is a globally recognized standard for information security management. In 2022, WORKAI® implemented an Information Security Management System (ISMS), and in 2023, it achieved ISO 27001 certification.
As part of our ISO 27001 certification, WORKAI® conducts regular risk assessments and develops corresponding risk treatment plans to mitigate any identified risks. This proactive approach allows us to continually enhance our security controls. The WORKAI® Security team consistently works towards improving the suitability, adequacy, and effectiveness of our ISMS.
Security and Privacy at WORKAI®
WORKAI® employs an Information Security Management System (ISMS) Officer and a Data Protection Officer (DPO). Their primary responsibility is to assess and implement security control measures throughout the organization.
Security Awareness Education
We offer our employees annual training in security awareness, coupled with regular updates on the latest security risks and the best practices to counter them. Every developer at WORKAI® receives consistent training on security to remain informed about prevalent security threats in development and to ensure the privacy of our customers’ data. Every WORKAI® employee and contractor is obliged to adhere to established security policies, which encompass confidentiality, data privacy, and incident reporting.
Assurance of Confidentiality
Confidentiality clauses are a standard feature in all customer agreements made by WORKAI®. Moreover, all WORKAI® employees and contractors must sign confidentiality agreements to safeguard customer data. We have similar confidentiality terms in place with all vendors handling personal or confidential customer information, which is part of our vendor evaluation process.
Incident Reporting and Management
All WORKAI® employees, contractors, and principal suppliers are obliged to report any security incidents. WORKAI® has a systematic plan to address any security or availability incidents swiftly and effectively. This incident response plan consists of three stages aimed at preventing, identifying, rectifying, and resolving security incidents.
Our incident response plan also includes a problem management process aimed at identifying root causes and resolving security-related incidents that were not previously identified. The entire Security Team is trained to effectively execute the established incident response plan. This plan is regularly assessed and updated to meet the requirements of ISO 27001 certification.
Contingency Planning and System Redundancy
WORKAI® has engineered a system aimed at reducing service disruptions due to natural disasters, hardware malfunctions, or other unexpected incidents or crises. Our approach to Disaster Recovery includes leveraging cutting-edge service providers to assist in delivering our services. Thousands of businesses trust these providers for their data and service delivery needs. Our disaster recovery program emphasizes technical disasters in the operation of the WORKAI® platform. It incorporates plans for various scenarios, enabling them to retrieve data during emergency situations.
Hosting within the European Union
Hosting within the European Union ensures that WORKAI®’s data is stored in a jurisdiction that adheres to the stringent EU privacy requirements and the General Data Protection Regulation (GDPR). By partnering with Microsoft Azure, a reputable cloud service provider, WORKAI® can take advantage of their EU-based servers, offering enhanced data protection measures. Microsoft Azure’s facilities comply with ISO 27001 standards, ensuring that WORKAI®’s data remains secure and in line with the strict privacy regulations of the EU.
Hosting outside the European Union
While WORKAI®’s servers could be hosted outside the European Union, it is crucial to consider the potential implications for data privacy and GDPR compliance. If WORKAI® chose a hosting provider located in a non-EU country, they would need to thoroughly assess and establish a legal framework to ensure the adequate protection of personal data. This could involve implementing appropriate safeguards such as standard contractual clauses or obtaining explicit user consent for cross-border data transfers. However, it is important to note that hosting outside the EU may pose challenges in meeting the specific requirements of GDPR and could potentially impact the level of data protection afforded to WORKAI®’s users.
Our Secure Development Lifecycle (SDLC) outlines the procedures and tools we leverage in software development and operations to heighten security. These techniques and resources are in line with recognized industry standards and corresponding frameworks.
Quality Assurance
To attain the utmost level of Quality Assurance (QA), we execute numerous automated tests on our foundational code. Moreover, every code alteration put forth by our developers is subjected to peer evaluation.
Isolated Environments
The testing and staging systems of WORKAI® are logically distinct from production systems. For testing purposes, WORKAI® generates exclusive test data.
Security Testing
WORKAI® collaborates with external penetration testing teams to conduct independent assessments at least once a year. As part of the assessment, WORKAI® utilizes the established Common Vulnerability Scoring System (CVSS) to determine the severity of any identified vulnerabilities.
Originating from the EU, WORKAI® has made privacy and data protection fundamental aspects of our product development, service offerings, and internal governance. Given that the EU enforces some of the most stringent data privacy laws globally, we incorporate our experiences in Europe into our methodology for building and developing employee communication tools.
Data Processing Agreements (DPA) in line with GDPR
WORKAI® provides its customers with Data Processing Agreements (DPAs) compliant with the General Data Protection Regulation (GDPR). Furthermore, as part of the supplier assessment process, WORKAI® enters into DPAs with all subcontractors processing personal data.
EU General Data Protection Regulation (GDPR) Compliance
WORKAI® complies with the requirements of the General Data Protection Regulation (GDPR) of the European Union, offering a secure communication platform that equally safeguards the data of employees and customers. The highest priority for WORKAI® is the right to privacy of its customers and employees, as well as the security of their personal data.
Our servers, which are all based within Microsoft Azure in Europe, possess the following certifications: ISO 27001:2013, ISO 27017:2015, ISO 27018:2014, ISO 20000-1:2011, ISO 22301:2012, ISO 9001:2015, and CSA STAR.
Physical storage is encrypted and, in addition, drives marked for replacement are securely repurposed using NIST 800-88 compliant methods.
Azure Services incorporate multi-layered mechanisms that ensure restricted access to client resources – protecting the Supervised Entity from unauthorized access by other users, including potential “malicious” clients of the service. Additional security features include notification mechanisms for any attempted inter-client environment access. Resources for clients are safeguarded, and measures are in place to prevent excessive resource allocation. A detailed description of the mechanisms employed can be found here.
The isolation is enforced at various levels, which include: